Program
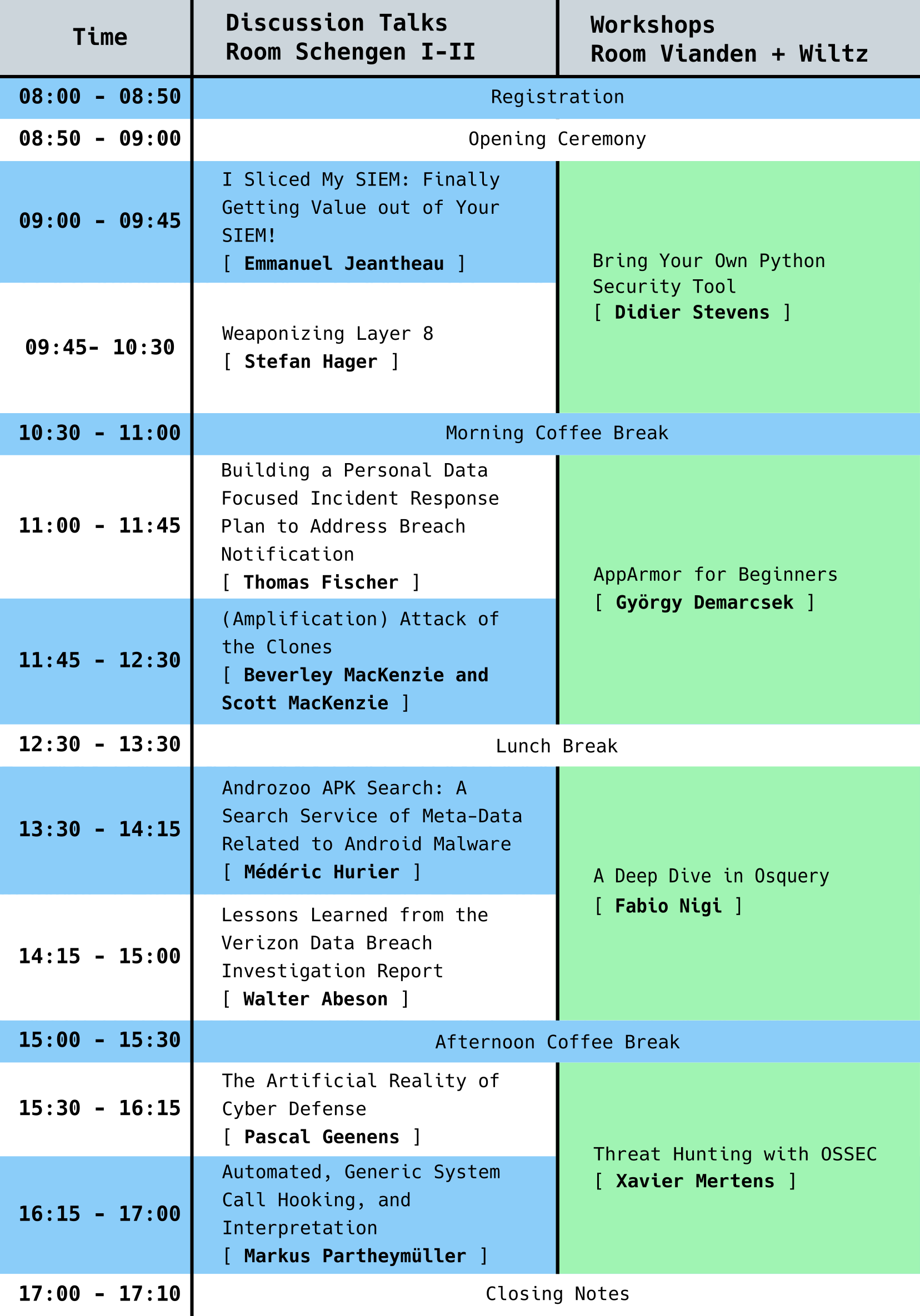
I Sliced My SIEM: Finally Getting Value out of Your SIEM!
SIEM history is linked to the evolution of the security industry. It has been designed initially to manage NIDS noise and then evolved to a correlation platform where outcomes of penetration test reports can be encoded. A couple of years ago, PCI-DSS and other regulations required "log analysis" to check the compliance box and companies matured in security incident response and forensics. SIEM was the natural answer for those needs. That lead many companies to invest (heavily) into SIEM technologies.
Nowadays when you talk to executives about SIEM the most common word used is "disappointment". It represents a lot of money and benefit is very low. This talk is about sharing experienced processes that can help any organization to get value out of the SIEM. It is NOT about new "shiny tools" or "easy tricks" that will increase the bill, but test proofed manageable processes that will help you to get the most out of your SIEM.
Keywords: SIEM, Blue Team, Efficiency, Streamline
Speaker
 |
Emmanuel JeantheauEmmanuel is an IT Security Enthusiast (SABSA & CISSP & ISO27001 & GCIH & GMON certified) with more than 10 years experience in this field, currently working for a cloud and security services provider. He is leading many security capabilities: Security Threat Monitoring, Threat Hunting, Security Incident Response and Active Defense. He is recognized by his peers for having a good mix of soft-skills and technical competencies. Before working in the Cloud Industry, Emmanuel worked for diverse industries - France Diplomacy; Decathlon (Sports retail); Société Générale & BNP Paribas (banks); Airbus (Aircraft Manufacturer) - He also owns of two master’s degrees (Security Telecommunication & Business Management). Emmanuel is always eager to connect with other IT Security Experts and hearing from former colleagues, managers, or just security creative folks, so do not hesitate to come to him to exchange about security topics! |
Weaponizing Layer 8
Do you think users are the weakest link in the security chain? Here is some duct tape to change that, and to raise the bar for social engineers and other attackers alike. Over the last few decades, sysadmins and people working in IT have called users names and generally rolled their eyes at the antics of those allegedly lazy, stupid and uneducated people.
From PEBKAC to ID-Ten-T we have been calling them names and didn't want them on our networks. This way of destructive thinking needs an overhaul, and here are some easy tricks on how users can become the valuable asset in corporate security that indeed they should be. Finding creative solutions to existing problems have been a standard skill for red teamers, whereas those defending networks often rely on standards.
Discover some creative solutions people have come up with to significantly raise their security - most of them are easy to implement - and how users can become a major asset of any security team.
Keywords: Creative Defense, Anti-phishing, Blue Team
Speaker
 |
Stefan HagerStefan works for the Internet Security Team at German company DATEV eG. Having started with computers and starting to be puzzled by reality in the 80s, he started out as a programmer in the early 90s. Since 2000 he has been securing networks and computers for various enterprises in Germany and Scotland. His main focus nowadays is raising security awareness, coming up with creative solutions to security problems and discussing new ideas concerning threat mitigation. When not trying to do any of the stuff mentioned above, he is either travelling, procrastinating or trying to beat some hacking challenge. Stefan also writes blog posts (in English and German) on his site https://cyberstuff.org. |
Building a Personal Data Focused Incident Response Plan to Address Breach Notification
The era of the data breach is upon us. In a traditional incident response investigation, the focus is often on attribution and how it was done, with an aim of quickly containing. Change needs to occur and organisations need to be able to quickly identify and understand what personal data is affected. Using the SANS six primary phases of incident response as a base, this talk will explore practical steps to rebuild the incident response plan with a personal data focus. By using and understanding Information Asset registries, data mappings and data protection impact assessments, the preparation phase can be enhanced to support personal data protection coverage in the IR plan. The goal to engage ideas and thoughts on how to improve the identification phase where detection and determination need to quickly identifies an event and subsequent incident where a potential personal data breach is occurring.
Keywords: Incident Response, Data Breach, Personal Data
Speaker
 |
Thomas FischerThomas has over 30 years of experience in the IT industry ranging from software development to infrastructure & network operations and architecture to settle in information security. He has an extensive security background covering roles from incident responder to security architect at fortune 500 companies, vendors and consulting organisations. He is currently a security advocate and threat researcher focused on advising companies on understanding their data protection activities against malicious parties not just for external threats but also compliance instigated. Thomas is also an active participant in the InfoSec community not only as a member but also as director of Security BSides London, ISSA UK chapter board member and speaker at events like SANS DFIR EMEA, DeepSec, Shmoocon, and various BSides events. |
(Amplification) Attack of the Clones
This talk looks at DOS and DDOS Attacks and how to mitigate them. Surveying how similar techniques of attack are cloned across different protocols, with different mitigating defence mechanisms that may be applied.
Consideration will be given to mitigate (D)DOS from old school Smurf and Fraggle, through newer DNS, NTP, SNMP reflection and amplification attacks. Moving up the stack to layer 7, to discuss the mitigation techniques to deal with various HTTP flood types of attack.
With Script kiddies using tools like RUDY, Slowloris, and various orbital ion cannons then clear strategies to defend against these threats are required. With botnets weaponised with various DOS munitions, along with the rise of Booters offering DDOS As A Service; it becomes essential to understand the tools and strategies required to survive the threat.
Keywords: DDOS mitigation, DDOS defence, Amplification Attack Prevention
Speaker
 |
Beverley MacKenzieBeverley has over 20 years’ experience working across many disciplines including Information Security, Audit, UNIX systems administration, Finance and Accounting. She is currently a Research Fellow at Abertay University, where in addition to teaching, she is working towards obtaining a Ph.D around Blockchain for the Internet of Things. |
Speaker
 |
Scott MacKenzieScott is currently contracted as a Senior IT Security Specialist to a global bank in Zürich working on the banks global Secure Key Management, PKI and cryptography systems. He has 22 years working in engineering, solutions, infrastructure, and enterprise security architecture. |
Androzoo APK Search: A Search Service of Meta-Data Related to Android Malware
We introduce Androzoo APK Search, an online service for querying structural information extracted from Android malware. The service is supported by an ElasticSearch cluster which can be leveraged by security experts to access a broad set of meta-data, including developer certificate information, source code elements, manifest information and antivirus labels collected for 1 million malicious applications. Androzoo APK Search can be accessed through a REST API and integrated with external projects via any HTTP clients.
Compared to other platforms, our solution supports a fast access model for retrieving the list of applications which match a specific feature (e.g., call to a given method name). Thus, our system enables the community to track indicators of compromise related to Android malware. With more than 900 fields extracted through static analysis, experts can also exploit the meta-data that we provide to devise better detection systems and prevent the propagation of malicious samples. Finally, Androzoo APK Search can be used to compute analytical metrics and create a baseline for the characterization and the classification of malware families.
Keywords: Android, Malware, Analysis, Online, Service
Resources: Talk
Speaker
 |
Médéric HurierMédéric works on Android Security, Big Data, Machine Learning, and Malware Analysis. He is a Ph.D. Student and Teacher Assistant at the University of Luxembourg. |
Lessons Learned from the Verizon Data Breach Investigation Report
You've heard about it, you've seen it cited, you may have even printed it, but have you actually read the Verizon Data Breach Investigation Report (VDBIR) in its entirety? If not, no worries! While the experience of curling up with a nice libation and the scintillating 70 pages of the VDBIR is quite enticing, come, hear a distilled version. Learn about the latest attack vectors, who the current cast of malicious actors are, and discover how to bolster your security posture against today's threat landscape. From human to technical exploits, internal to external agents, acquire the knowledge that's necessary to defend yourself against the threats that matter most.
Keywords: Blue Team; Defense; Threat Intelligence
Resources: Talk
Speaker
 |
Walter AbesonWalter Abeson is currently a Systems Engineer with RSA NetWitness, focusing on digital forensics, incident response, and threat hunting. Walter thrives at detecting anomalous behavior in both endpoint and network environments. Prior to joining RSA, Walter was the Technology Manager for Black Hat, responsible for the NOC and overall security posture. Walter continues to serve as staff for the Black Hat NOC and is also a goon at DEF CON. When not behind a computer, Walter enjoys photography, reading, and spending time outdoors. |
The Artificial Reality of Cyber Defense
Security threats are growing faster than security teams and budgets while there is a huge talent shortage in security. The proliferation of data from dozens of security products in complex environments is paradoxically making it harder, not easier, for teams to detect and investigate threats.
Attackers already have an unfair advantage over the defenders in cyber-attacks, it's time for security strategies to leverage automation in detection and mitigation, restore the balance and increase our chances to come out on top in the war against cyber threats. This presentation will discuss the different options in automating the detection and mitigation of attacks, from traditional machine learning to advanced deep learning systems, their challenges, and applications, and where they fit in a modern cybersecurity strategy.
Keywords: AI, Machine Learning, Deep Learning, Cyber Security, Anomaly Detection, Automation
Speaker
 |
Pascal GeenensAs the EMEA Cyber Security Evangelist for Radware, Pascal is a recognized Cyber Security and Emerging Technology thought leader with 20+ years of experience in Information Technology. While executing Radware’s thought leadership on today’s security threat landscape, Pascal leads the research efforts on IoT botnets and discovered BrickerBot and JenX botnets. Pascal holds a degree in Civil Engineering from the Free University of Brussels. Prior to Radware, Pascal was a consulting engineer for Juniper working with the largest EMEA cloud and service providers on their SDN/NFV and data center automation strategies. |
Automated, Generic System Call Hooking, and Interpretation
When doing malware analysis, monitoring application behavior plays an essential role. To do that, one of our most used mechanisms is system call monitoring. In contrast to approaches that e.g. put breakpoints into mapped libraries, we employ a VM monitor approach that catches the SYSCALL instruction itself. When interrupting processes on such instructions, what syscall did they actually attempt to use and what do the parameters mean, as it’s all encoded in CPU registers or the stack? In order to solve that problem in the most elegant way for our users, we needed a library of signatures of all syscalls along with the data structure types and formats they use. We automated the process of harvesting system calls and data structure definitions from multiple public open-source sources and preprocessing them to produce a single data source in machine-readable form. We present the results that we keep OSS to share with the community, and demonstrate how this improves the analyst workflow.
Keywords: Process Monitoring, Virtualization, System Calls, System Call Signatures, Automation, Open Source
Speaker
 |
Markus PartheymüllerMarkus has been working with the Intel x86 architecture and virtualization technology since his college days. After working at Intel Labs and FireEye, he co-founded the Cybersecurity startup Cyberus Technology, where he is one of the core developers of their own secure virtualization technology stack. Markus is interested in making malware analysis simpler by combining analysis tools with the power of virtualization technology in ways that are simple to use and easy to automate. He is also an open source enthusiast. He received his Diploma in Computer Science at TU Dresden, Germany. |
Bring Your Own Python Security Tool
Didier Stevens, seasoned developer of security tools, will show you the basics of Python security tools and the concepts behind his tools. You are invited to bring your own Python security tools, to be debugged/adapted/improved during this workshop.
Keywords: Python, Tools, Security
Resources: Slides
Speaker
 |
Didier StevensDidier Stevens (Microsoft MVP, SANS ISC Handler, Wireshark Certified Network Analyst, CISSP, GSSP-C, GCIA, GREM, MCSD .NET, MCSE/Security, MCITP Windows Server 2008, RHCT, CCNP Security, OSWP) is a Senior Analyst (NVISO). Didier is a pioneer in malicious PDF document research and malicious MS Office documents analysis and has developed several tools to help with the analysis of malicious documents like PDF and MS Office files. You can find his open source security tools on his IT security related blog. |
AppArmor for Beginners
In this workshop, we are going to explore how AppArmor can be used to sandbox processes on Linux in practice in order to limit attack surfaces and mitigate post-exploitation scenarios. There will be a short theoretical introduction after which we will cover the following practical tasks and topics:
- Checking AppArmor status and related kernel parameters
- Loading AppArmor and policies at boot time
- Checking the security context of running processes
- Creating AppArmor profiles using automated tools (aa-autodep, aa-genprof, aa-logprof, etc.)
- Basics of the AppArmor profile language
- Understanding and using common profile abstractions (/etc/apparmor.d/abstractions)
- Inspecting and interpreting AppArmor logs (for debugging and monitoring)
- Basic profile management tasks and utilities (aa-enforce, aa-complain, aa-disable, apparmor_parser, etc.)
After completing these smaller exercises, we are going to write a profile for a Python web application that uses a vulnerable third-party CLI (ImageMagick/convert) tool. We will see how we can use AppArmor to immunize our web application to certain vulnerabilities in third-party components and inside the web service itself.
We are going to learn how the AppArmor userspace API (aa_change_profile and aa_change_hat) can be used to implement privilege separation, further improving the security of our application.
Assumed background knowledge: basic understanding of Linux and system calls, basic literacy in C and Python
Required tools: Oracle VirtualBox and Hashicorp Vagrant.
The Vagrant box for the workshop will be available for download here (from 15 October). If you can, please download it in advance. Latest versions of both Vagrant and VirtualBox are suggested.
Keywords: AppArmor, Linux, MAC, LSM, Python
Resources: Slides
Speaker
 |
György DemarcsekGyörgy Demarcsek currently works as a security engineer at IBM Budapest Lab (previously Ustream). Previously, he worked in the same position at Prezi.com and as a technical student at CERN. He enjoys working in the intersection of software engineering and IT security and he likes fiddling with OS-level vulnerabilities and mitigations, especially interested in sandboxing technologies. |
A Deep Dive in Osquery
We will see how Osquery works, and how to use it to protect your environment. During the workshop, we will demonstrate how to collect and track down IOCs in an investigation scenario from processes running without a binary on disk to Yara rules integration. By the end of the workshop, you will understand how to deploy Osquery on a global scale, and how to integrate the right plugins and community projects.
Keywords: Osquery, Endpoint Protection, Endpoint Incident Response, Automation
Resources: Slides
Speaker
 |
Fabio NigiFabio Nigi is building a CSIRT for a major Belgian engineering company, and he is a former security investigator at Cisco CSIRT. During and after his engineering degree in Computer Science, Fabio focused on Ethical Hacking, spent 10 years researching, analyzing and solving ICT Governance, Risk, Compliance, Information Security and Privacy issues as subject matter expert in enterprise environments. |
Threat Hunting with OSSEC
OSSEC is sometimes described as a low-cost log management solution but it has many interesting features which, when combined with external sources of information, may help in hunting for suspicious activity occurring on your servers and end-points. During this workshop, you will learn the basic of OSSEC and its components, how to deploy it and quickly get results. Then I will demonstrate how to deploy specific rules to catch suspicious activities. From an input point of view, we will see how easy it is to learn new log formats to increase the detection scope and, from an output point of view, how we can generate alerts by interconnecting OSSEC with other tools like TheHive or an Elastic Stack/Splunk/etc.
Keywords: OSSEC, Logs, Threat Hunting, Security, Integration
Resources: Slides
Speaker
 |
Xavier MertensXavier Mertens is a freelance cybersecurity consultant based in Belgium. His daily job focuses on protecting his customer’s assets by applying “offensive” (penetration testing) as well as “defensive” security (incident handling, forensics, log management, SIEM, security visualization, OSINT). Besides his daily job, Xavier is also a security blogger (https://blog.rootshell.be), a SANS Internet Storm Center handler (https://isc.sans.org) and co-organizer of the BruCON (http://www.brucon.org) security conference. |